Endpoint Monitoring and Threat Detection
See what’s happening on your endpoints, detect intrusions fast. Spear phishing attacks can quickly lead to compromised endpoints. External intrusions can result from unpatched systems or zero day attacks. We provide deep, real-time visibility into endpoint and server activities. We detect intrusions and suspicious activity through machine learning and behavioral analytics. Don’t let hosts remain compromised.
Stay a Step Ahead
Expose Advanced Malware
Advanced malware can easily evade traditional endpoint protection solutions. We’ll alert when the malware goes active by detecting behavioral anomalies on the compromised host.
Quickly See Malware Outbreaks
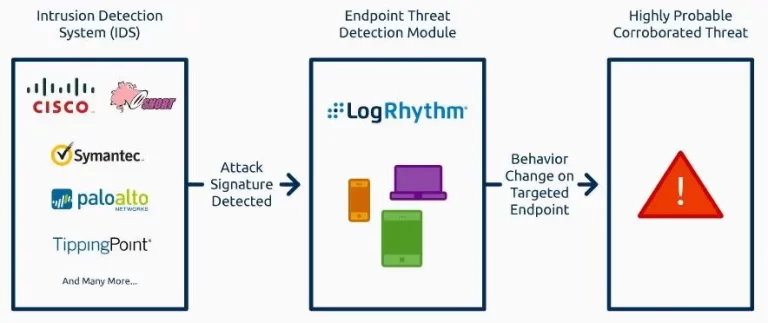
Left undetected, malware can quickly propagate across your network. We integrate with a variety of endpoint protection platforms to ensure at the first sign of an outbreak, you become immediately aware.
Detect Unauthorized File and Registry Changes
Whether the result of an attack, or change management gone awry, we’ll detect changes to sensitive files and registry settings. Learn more about File Integrity Monitoring.
Detect Zero-Day Attacks
If an attacker comes at you with a zero-day, intrusions are going to occur. Our analytics will expose the compromise, preventing the attacker from expanding their foothold.
Stop Lateral Movement
Once a threat controls an endpoint, they’ll use it to launch additional attacks. We’ll detect abnormal communication patterns, uncovering the compromise, preventing further damage.
Expose Data Theft
Attackers use your endpoints against you to transfer stolen data to external sites or locally writable media. We’ll detect behaviors indicative of data exfiltration, and can automatically kill transfers using SmartResponse.
Endpoint Protection and Response
Dig Deeper, Detect Faster
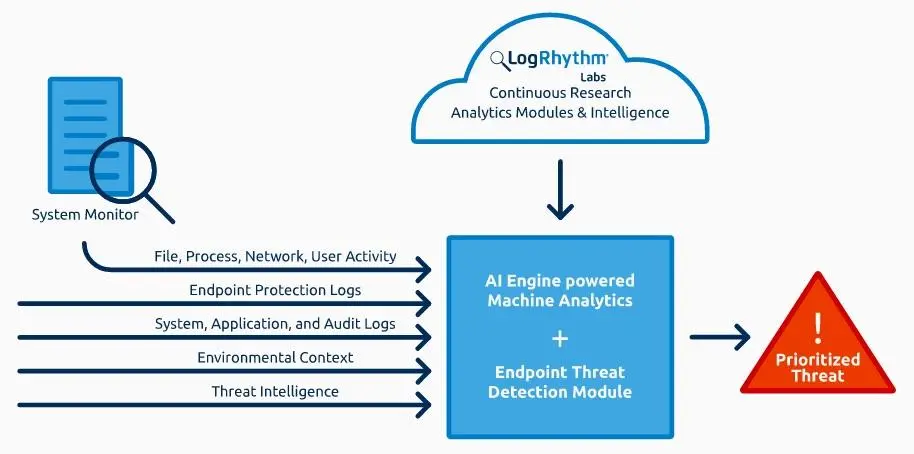
The quality of your data dictates the richness of analytics-driven intelligence. Combine System Monitor with our Endpoint Threat Analytics Module to realize the most comprehensive endpoint behavioral analytics solution available. Advanced threats are more accurately detected. Incident responders are better enabled with access to high fidelity forensic date, generated in real-time.
Know What’s Normal—and What’s Not
Additional Resources
If you would like more information on LogRhythm, contact us today!