IBM QRadar
The threat detection and response suite built to help your security teams outsmart threats with speed, accuracy and efficiency
Outsmart attacks with a connected, modernized security suite
IBM Security® QRadar® Suite is a modernized threat detection and response solution designed to unify the security analyst experience and accelerate their speed across the full incident lifecycle. The portfolio is embedded with enterprise-grade AI and automation to dramatically increase analyst productivity, helping resource-strained security teams work more effectively across core technologies. It offers integrated products for endpoint security (EDR, XDR, MDR), log management, SIEM and SOAR—all with a common user interface, shared insights and connected workflows.
Benefits
Unified analyst experience
Cloud delivery, speed and scale
Open platform and pre-built integrations
QRadar products
QRadar® SIEM
The market-leading QRadar SIEM is now available as a service on AWS, enhanced with the new unified analyst interface that provides shared insights and workflows with broader security operations toolsets. By using AI, network and user behavior analytics, along with real-world threat intelligence, analysts are now empowered with more accurate, contextualized and prioritized alerts.
QRadar® EDR
Protect your endpoints against previously unknown zero-day threats using automation and hundreds of machine learning and behavioral models to detect anomalies and respond to attacks in near real time. By using a unique approach that monitors operating systems from the outside, organizations can now avoid manipulation or interference by adversaries.
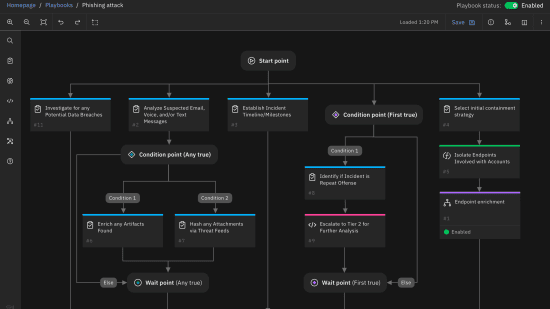
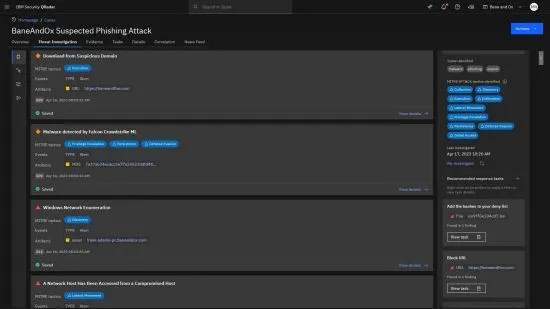
QRadar® SOAR
Recent winner of a Red Dot Design Award for interface and user experience, QRadar SOAR helps organizations automate and orchestrate incident response workflows and ensure their specific processes are followed in a consistent, optimized and measurable way.
QRadar® Log Insights
QRadar Log Insights is a cloud-native log management and security observability product that provides simplified data ingestion and rapid search, investigations and visualizations. By using an elastic security data lake, analysts can now perform analytics on terabytes of data with greater speed and efficiency.

Features
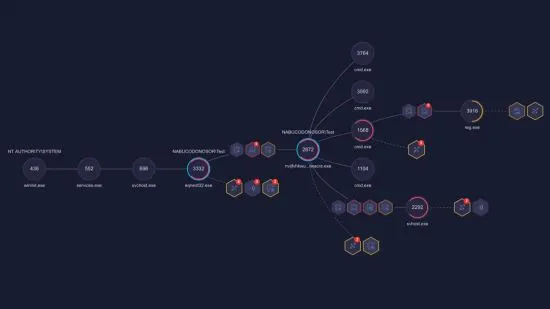
Threat investigation
Threat Investigator works with Case Management to find cases that warrant an investigation and automatically starts investigating. The investigation fetches artifacts attached to the case and starts data mining. After Threat Investigator completes several rounds of data mining, it generates a timeline of the incident that consists of MITRE ATT&CK tactics and techniques plus a chain graph of the incident.
Delivered as SaaS on AWS
The SaaS on AWS delivery method allows you to get up and running quickly, without the need for ongoing updates or management. It enables you to focus on patching important vulnerabilities and reviewing anomalous conditions.
Federated search
Federated search allows you to search data in the cloud or on premises in a single, unified way. You can break down data silos and unlock cross-functional insights with an intuitive search experience that requires no data movement, freeing up IT resources.
Data collection
Data collector makes it possible to get telemetry data set up and ingest with just a few clicks. It supports many protocols, including passive and active. Passive protocols listen for events on specific ports while active protocols use APIs or other communication methods to connect to external telemetry that poll for events.
Detection and response center
The center streamlines the adoption of new use cases by centralizing management of detection and response use cases, reducing complexity and improving efficiency. You can use rules management across cloud or on premises to view, create and adjust with the easy-to-use rule editor.
Unified user experience
Integrating across EDR and XDR, Log Insights, SIEM and SOAR products helps you make faster and more accurate decisions. Insights and actions are automatically provided across investigation and response workflows, including the ability to automatically enrich artifacts with threat intelligence, create cases and recommended responses.